Oracle published an out-of-band security alert for a critical vulnerability in Oracle Identity Manager and Oracle Web Services Manager, following in-the-wild exploitation of a related flaw in the same component in November 2025.
Key takeaways:
- CVE-2026-21992 is a critical remote code execution vulnerability in Oracle Identity Manager and Oracle Web Services Manager with a CVSSv3 score of 9.8.
- The vulnerability is remotely exploitable without authentication, and Oracle issued an out-of-band security alert outside of its regular quarterly Critical Patch Update cycle.
- A related vulnerability in Oracle Identity Manager’s REST WebServices component, CVE-2025-61757, was exploited in the wild and added to CISA’s KEV catalog in November 2025.
Background
On March 19, Oracle published an out-of-band security alert for a critical vulnerability in two Oracle Fusion Middleware products:
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2026-21992 | Oracle Fusion Middleware Remote Code Execution Vulnerability | 9.8 |
Oracle rarely issues out-of-band security alerts, reserving them for vulnerabilities that warrant attention outside of its quarterly Critical Patch Update (CPU) cycle. The next scheduled CPU is April 2026.
Analysis
CVE-2026-21992 is a remote code execution vulnerability affecting two Oracle Fusion Middleware products: Oracle Identity Manager and Oracle Web Services Manager. An unauthenticated, remote attacker could exploit this vulnerability over HTTP to achieve code execution on a vulnerable system. The vulnerability has a CVSSv3 score of 9.8.
The vulnerability affects different components in each product. In Oracle Identity Manager, the affected component is REST WebServices. In Oracle Web Services Manager, the affected component is Web Services Security.
Out-of-band advisory signals elevated risk
Oracle describes its Security Alerts as fixes “deemed too critical to wait for distribution in the next Critical Patch Update.” Oracle has issued approximately 31 Security Alerts since 2010, averaging about two per year. The decision to release CVE-2026-21992 as an out-of-band Security Alert rather than waiting for the next quarterly CPU in April 2026 is significant.
This is only the second out-of-band Security Alert Oracle has issued for Oracle Identity Manager. The first, CVE-2017-10151, was a CVSS 10.0 default account vulnerability that allowed complete compromise of Identity Manager via an unauthenticated network attack.
The urgency may be related to CVE-2025-61757, a pre-authentication RCE in Oracle Identity Manager patched in Oracle’s October 2025 CPU and added to CISA’s Known Exploited Vulnerabilities (KEV) catalog in November 2025.
Researchers at Searchlight Cyber published details describing CVE-2025-61757 as an authentication bypass in Identity Manager’s REST WebServices component, calling it “somewhat trivial and easily exploitable by threat actors.” While CVE-2026-21992 affects the same product, component and versions, Oracle has not confirmed whether the two are related. Oracle has also not disclosed whether CVE-2026-21992 has been exploited in the wild.
Historical exploitation of Oracle Fusion Middleware vulnerabilities
Oracle Fusion Middleware has six vulnerabilities in CISA’s KEV catalog. Oracle has 42 total entries across all products in the catalog.
| CVE | Description | Date Added |
|---|---|---|
| CVE-2025-61757 | Oracle Fusion Middleware Missing Authentication Vulnerability (Identity Manager) | 2025-11-21 |
| CVE-2021-35587 | Oracle Fusion Middleware Access Manager Takeover Vulnerability | 2022-11-28 |
| CVE-2020-2551 | Oracle Fusion Middleware WebLogic Server Vulnerability | 2023-11-16 |
| CVE-2012-1710 | Oracle WebCenter Forms Recognition Vulnerability | 2022-05-25 |
| CVE-2012-0518 | Oracle Application Server Single Sign-On Vulnerability | 2022-03-28 |
| CVE-2012-3152 | Oracle Fusion Middleware Reports Developer Vulnerability | 2021-11-03 |
Proof of concept
At the time this blog post was published, there was no public proof-of-concept (PoC) available for CVE-2026-21992.
Solution
Oracle has released patches for the following affected products:
| Affected Products | CVE | Affected Versions |
|---|---|---|
| Oracle Identity Manager | CVE-2026-21992 | 12.2.1.4.0, 14.1.2.1.0 |
| Oracle Web Services Manager | CVE-2026-21992 | 12.2.1.4.0, 14.1.2.1.0 |
Patch details are available through the Patch Availability Document for Fusion Middleware.
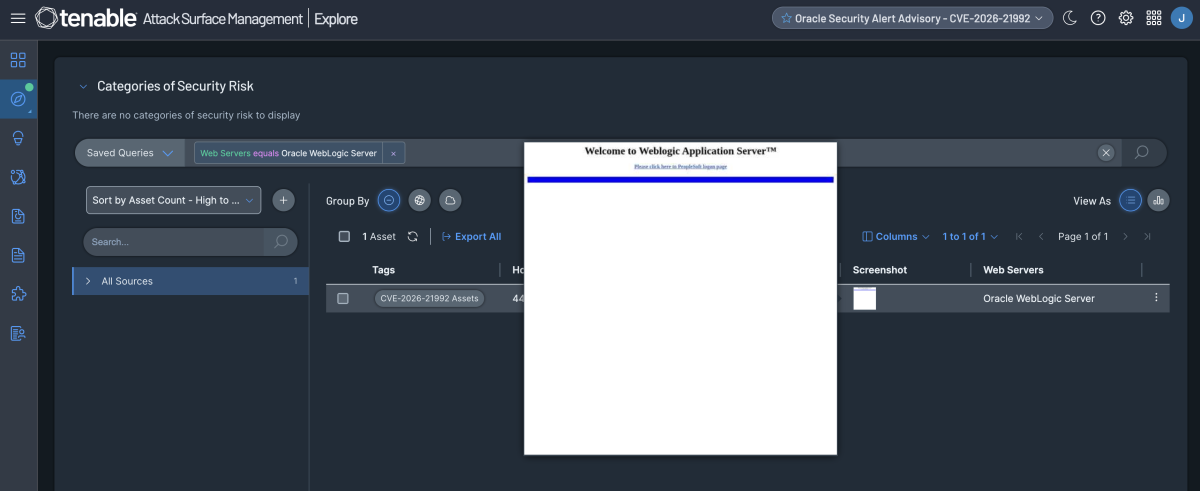
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2026-21992 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets using the following query: Web Servers equals Oracle WebLogic Server
Get more information
- Oracle Security Alert Advisory – CVE-2026-21992
- Breaking Oracle’s Identity Manager: Pre-Auth RCE (CVE-2025-61757)
Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect and engage with us in the Threat Roundtable group for further discussions on the latest cyber threats.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.